There Is A War Going On For Your Mind: The Science and Logic Behind MK-Ultra
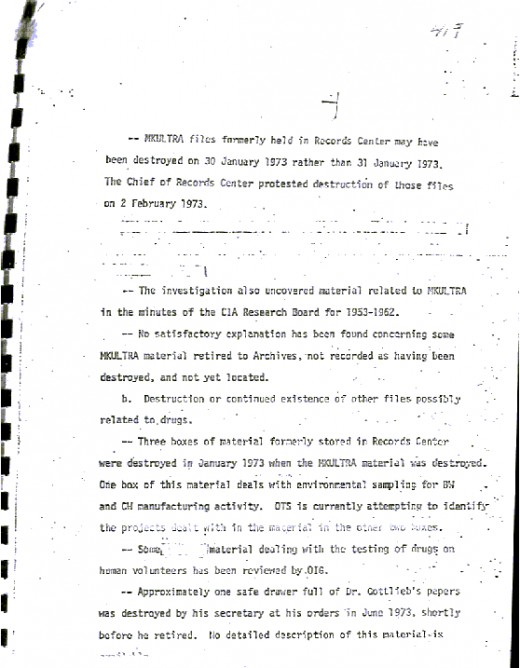
Declassified MK-Ultra Documents
Amidst the dying controversy of Nazi eugenic practices and the newfound rumors of Russian psychological experimentation, the CIA invoked the innovations of the former and the possible threat of the latter in order to create the perfect defensive and offensive weapon: a mind controlled assassin, or “Manchurian Candidate” (Marks 9). Initiated in 1953 by the CIA, Project MK-ULTRA began its eleven-year program directed towards behavioral modification through the means such as physical trauma, heavy drug usage, as well as visual and audio stimulation (Lett 250). MK-ULTRA soon served as an umbrella classification over a number of notable sub-projects, including one of the most impacting, yet least known branches, Project Monarch. This plan, directed by Dr. George Estabrooks, sought to create a hypnotically controlled individual through personality splicing (Keith 74). Built upon a scientific basis, this trauma-based mind control was and may continue to be the effective means of manipulating the individual, who in turn will impact the masses.
Project Monarch attributes its name to the monarch butterfly, whose metamorphosis is representative of the splitting of an individual’s personality, resulting in Dissociative Identity Disorder, wherein two or more distinct identities are present within one individual (Yeadon 402). The want for personality splicing is due to the ability for created and programmed identities to take control over a person’s behavior, which then cannot be remembered by the original state of the individual suffering these experiences.
The creation of multiple personalities is the result of several levels of programming. The first, described by Jim Keith, author of Mass Control: Engineering Human Consciousness, involves “generalized mind control, the base level programming of the subject, and characterized by augmented memory and the splitting of the mind into left and right brain divisions” (38). This fission of the mind is then re-structured through neuron pathway stimulation, which is instigated by a “trigger”, an object or sound of some sort. The recognition of the trigger then prompts the manipulated connection between the two hemispheres of the brain (Hundall 11).
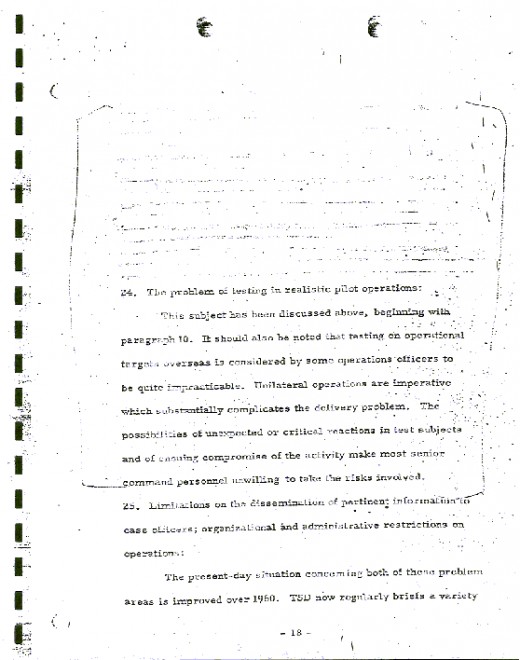
The second stage of Project Monarch entails the purposeful elimination of any learned moral convictions or inhibitions, which allows for the following stage, loosely termed as the “killer” program, to develop within the individual, fearless and systematic behavior (Hundall 11). The same methods generally used in training the United States special operations, including Delta Force, are then instilled upon the individual. Adrenal output and aggression become perfectly controlled, and self-destruct instructions are introduced (Patton 5).
The final level that the individual under submission attains is termed as the “self-destruct” phase. Instruction hereby dictates suicide if interrogation occurs, awareness of events develop, or psychological therapy is pursued. Deceptive programming is sometimes injected as an alternative to the self-destruct phase, or in conjunction with it, causing the individual to produce misleading misinformation when interrogated. Still, the phase of deception is used far less than that demanding suicide (Keith 39).
Project Monarch as a whole is thereafter “updated periodically and reinforced through visual, auditory, and written mediums” meant for desensitizing the general populace while subliminally stimulating the victims of programming. Prime examples of this continued conditioning is still prevalent in current American culture. Literature, mainly The Catcher in the Rye, films such as Alice in Wonderland, and songs including Helter Skelter by the Beatles have been attributed as creations meant for the sole intention of preserving the MK-ULTRA indoctrination (Patton 6).
While the initial programmer of Project Monarch cannot be identified, allegations have been made towards a number of federal and medical personnel, who performed the majority of these mind experiments in the walls of universities, including Duke, Princeton, and UCLA. The amount of evidence for the actual existence of these traumatic programs is steadily increasing, with Dissociative Identity Disorder rising from a barely noteworthy diagnosis, pertaining to perhaps twenty patients in 1980, to a common occurrence only ten years later, with 250,000 noted instances, as well as Bill Clinton’s open apology during his presidency for all past ethical atrocities (Hatton 187). Still, one must wonder on how manifest the essence of MK-ULTRA remains within countless components of modern society.
Copyright Lilith Eden 2011. All Rights Reserved.
Works Cited
Yeadon, Glen. The Nazi Hydra in America: Suppressed History of a Century. Lulu.com, 2008. Print.
Hudnall, Ken. Manhattan Conspiracy: Blood on the Apple. Omega Press, 2004. Print.
Keith, Jim. Mass Control: Engineering Human Consciousness. Adventures Unlimited
Press, 2003. Print.
Patton, Ron. The Conspiracy Reader. Citadel Press, 1999. Print.
Hatton, Gyeorgos. Changing Perspectives. Phoenix Source Distributors, Inc., 1994. Print.
Lett, Donald. Phoenix Rising: The Rise and Fall of the American Republic. Phoenix Rising, 2008. Print.